Why is Rust Safer than C? A Comprehensive Comparison for Systems Programming
This analytical guide explains why is rust safer than c in memory safety, concurrency, and tooling, with practical guidance for developers tackling system programming.

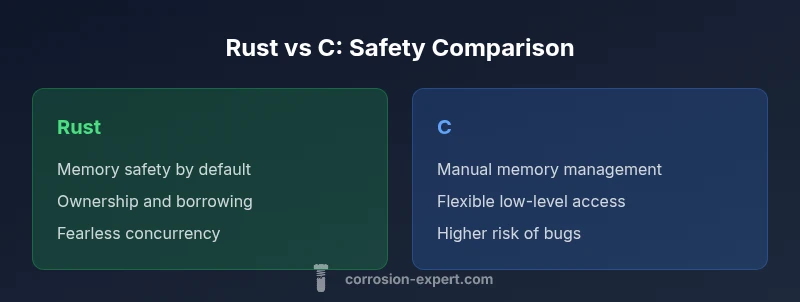
Why is rust safer than c? The short answer is that Rust enforces memory safety at compile time through ownership, borrowing, and lifetimes, preventing common bugs such as use-after-free and buffer overflows. It also ensures thread safety with fearless concurrency and strict type guarantees. C, by contrast, relies on manual memory management and programmer discipline, which often causes runtime errors and security vulnerabilities.
Why safety concepts matter in systems programming
In low-level systems work, safety isn't optional—it's the foundation that prevents catastrophic failures. According to Corrosion Expert, safety in software is as critical as material integrity in metalwork. The question often comes down to a simple consideration: why is rust safer than c? The answer begins with memory safety guarantees that stop many classes of bugs before they run. Rust enforces strict rules at compile time about who owns what, how long data lives, and when references can be shared. This transforms safety from an afterthought into a design constraint. C provides power and flexibility, but it lets the programmer decide where memory is allocated or deallocated. Without rigorous discipline, you may encounter buffer overflows, use-after-free bugs, and undefined behavior that are notoriously hard to track in large codebases. The contrast isn't merely theoretical: it impacts maintainability, security, and reliability across embedded devices, operating system components, and performance-critical services. Teams choosing Rust over C often report fewer remediation cycles, easier reasoning about code movement across threads, and fewer surprises when extending systems. The central thesis remains: safety features matter for long-term stability, and that is a central reason why is rust safer than c in practical terms.
Core safety mechanisms in Rust
At the core of Rust's safety model are ownership, borrowing, and lifetimes. Ownership enforces a single owner for each value, preventing double frees. Borrowing allows multiple readers or one writer with strict rules, preventing data races. Lifetimes ensure references are valid for the duration they are used, eliminating dangling pointers. The language makes these constraints explicit in type signatures and compiler errors, so many safety issues are caught before compilation completes. The compiler guides developers toward safe patterns, and cargo-based tooling enforces consistent formatting, linting, and testing. In the broader context of why is rust safer than c, this design reduces the cognitive burden of memory management. The safety net is reinforced by safe abstractions that still compile to highly efficient machine code, enabling both performance and correctness to scale together. While unsafe blocks exist for low-level operations, their use is explicit and isolated, preserving overall safety while offering necessary flexibility for systems programming. This balance is a key reason why is rust safer than c in countless real-world scenarios, from device firmware to high-performance servers.
How C handles memory safety and its risks
C offers unmatched control over memory and hardware, which is precisely why it remains widely used in performance-critical domains. However, this power comes with significant risk: manual memory management makes it easy to forget to free memory, mismanage allocations, or dereference null or freed pointers. Buffer overflows, off-by-one errors, and use-after-free bugs are common culprits that can lead to crashes or security vulnerabilities. C lacks automatic bounds checking, and there is no compile-time guarantee that every pointer is valid or that data lives long enough for the context. The result is that many safety issues surface only at runtime, after deployment, in production systems and critical security components. This reality underscores the contrast in why is rust safer than c: Rust's safety-first approach aims to prevent many of these bugs at compile time, whereas C leaves room for human error. Developers migrating from C to Rust typically gain a more predictable safety profile, even when they still perform low-level optimizations. The transition demands an adjustment to design patterns, memory ownership thinking, and a different mentality about resource lifecycles. For teams that prioritize reliability, the cost of this mental shift is often outweighed by long-term maintenance and security benefits.
Concurrency and data access patterns
Concurrent programming in C is possible but perilous without careful discipline, tooling, and rigorous testing. Data races can emerge when multiple threads access shared state without proper synchronization, leading to subtle, hard-to-reproduce bugs. Rust’s concurrency model enforces thread safety by design through Send and Sync traits, which indicate whether a type can be safely transferred between threads or shared across them. The compiler checks these properties, reducing the likelihood of data races and race conditions at compile time. This is a fundamental factor in why is rust safer than c: it turns concurrency from a manual, error-prone pattern into a safer, more predictable workflow. In practice, Rust encourages you to structure shared state with message passing, immutable data by default, and carefully chosen synchronization primitives. While C can achieve similar guarantees, it requires extensive discipline, external libraries, and rigorous manual audits. The Rust approach lowers the probability of introducing unsafe concurrency into production while preserving performance through parallelism that is both safe and efficient. When projects demand scalable parallelism, the Rust model often proves superior to C’s ad-hoc methods.
Tooling and compile-time checks
Rust’s tooling ecosystem—Cargo for project management, rustc for compilation, Clippy for linting, and Rustfmt for formatting—creates an integrated safety-first workflow. These tools encode best practices, automatically catch common mistakes, and enforce consistent coding standards. The compiler provides detailed error messages that guide developers toward safer patterns, which is instrumental when evaluating why is rust safer than c in a modern toolchain. In contrast, C tooling varies widely by compiler and platform; memory-safety checks rely heavily on runtime testing, static analysis, and third-party libraries. This fragmentation can obscure safety guarantees, especially in large or long-lived codebases. By adopting Rust tooling, teams benefit from a cohesive, opinionated perspective on safety, reproducible builds, and automated testing pipelines. The payoff is not only fewer bugs but faster onboarding of new developers who can rely on the toolchain to enforce correct practices.
Performance and safety: trade-offs
A common concern is whether safety features slow you down. In reality, Rust emphasizes zero-cost abstractions, meaning safe abstractions incur minimal runtime overhead. The ownership model and borrow checker catch inefficiencies and prevent unsafe patterns before they can run, often improving performance predictability. In some rare scenarios, you may encounter compile-time checks that require refactoring of algorithms, but the payoffs are safer execution and easier maintenance. C can achieve similar performance, but at the cost of greater risk if code quality slips. When designing performance-critical systems, teams frequently evaluate the cost of safety features against the potential consequences of memory-corruption bugs. Most find that Rust’s model delivers comparable performance for typical workloads while significantly reducing the risk surface. In short, safety and performance do not have to be mutually exclusive, and why is rust safer than c in real-world benchmarks often reflects this balance.
Learning curve and ecosystem considerations
Adopting Rust involves a learning curve, particularly around ownership, borrowing, and lifetimes. Developers comfortable with C may initially struggle with the stricter compile-time checks, yet many report accelerated long-term productivity as they internalize safe patterns. The ecosystem offers modern tooling, comprehensive documentation, and active community support that accelerates mastery. Rust’s ecosystem continues to grow in domains like systems programming, embedded, and performance-critical software, while C remains entrenched in legacy code and highly optimized libraries. The decision factors for why is rust safer than c at the organizational level often hinge on team readiness, project timelines, and long-term maintenance expectations. Training programs, mentorship, and incremental adoption strategies can ease the transition, letting teams preserve performance while elevating safety.
Real-world implications: safety in embedded and systems
In embedded and operating-system domains, safety is paramount. Rust’s safety guarantees help prevent memory errors that historically plagued low-level firmware, drivers, and kernel modules. This translates into fewer crash scenarios, reduced security vulnerabilities, and more predictable hardware interactions. However, the decision to adopt Rust in such contexts must consider existing toolchains, hardware constraints, and compatibility with existing C libraries. The payoff is a safer codebase that remains close to hardware while benefiting from safer abstractions and modern tooling. When comparing long-term risk, development velocity, and post-deployment reliability, many teams find that why is rust safer than c is evident in the robust safety model that Rust provides, especially for new system components and greenfield projects.
When C remains relevant despite safety features
There are legitimate reasons to continue using C in certain situations. Legacy codebases, extreme resource constraints, and well-established toolchains can make C a practical choice. Interoperability with existing libraries and hardware interfaces can require continued C usage, and some safety-critical domains rely on formally verified C components or a mixture of C and Rust. The decision should weigh the cost of rewriting versus the benefits of Rust’s safety model, taking into account team expertise, maintenance overhead, and project risk. For teams evaluating why is rust safer than c, the answer often centers on a phased adoption plan: start with critical safety components in Rust while maintaining legacy C where necessary, gradually migrating as confidence and tooling mature.
Comparison
| Feature | Rust | C |
|---|---|---|
| Memory Safety (compile-time guarantees) | Strong safety by default; no null pointers in safe code | Manual memory management; risk of null dereferences and overflows |
| Borrowing/Ownership Model | Enforced at compile time; prevents use-after-free and data races | No ownership semantics; potential for aliasing and leaks |
| Concurrency Safety | Fearless concurrency via Send/Sync; data races minimized | Prone to data races without careful synchronization |
| Unsafe Operations | Explicit unsafe blocks; safe by default with opt-in risks | No explicit safety boundary; undefined behavior possible |
| Tooling & Safety | Cargo, Clippy, rust-analyzer; strong safety tooling | Tooling varies by compiler; safety relies on practices |
| Performance & Abstraction | Zero-cost abstractions; safety doesn't cost performance | Low-level control can yield high performance but increases risk |
| Learning Curve | Steep at first due to ownership concepts | C is simpler syntax but safety relies on discipline |
| Domain Adoption | Growing in OS, embedded, and high-performance apps | Legacy systems and some domains rely on C |
The Good
- Safer defaults reduce maintenance risk
- Modern tooling and strong compile-time checks
- Predictable performance with zero-cost abstractions
- Improved safety in concurrency and memory access
- Better long-term return on safety investments
Cons
- Steeper learning curve for beginners
- Longer initial compile times in large projects
- Interop with legacy C can be complex
Rust generally offers safer system programming with strong safety guarantees; C remains viable for legacy and ultra-low-level work.
For new projects prioritizing safety and maintainability, Rust provides clear advantages. Choose C when legacy integration, hardware constraints, or existing tooling dominate the decision, then migrate progressively where feasible.
Quick Answers
What makes Rust fundamentally safer than C?
Rust enforces memory safety at compile time through ownership, borrowing, and lifetimes, preventing many common bugs. It also provides safer concurrency, reducing data races. This contrasts with C, where memory management and manual synchronization can lead to errors that surface in production.
Rust provides memory safety and safer concurrency by design, unlike C where memory errors and data races are common risks.
Can Rust completely eliminate memory safety bugs?
Rust greatly reduces memory safety bugs by default, but unsafe blocks exist for advanced low-level work. When used carefully, the safety guarantees remain strong. No language can guarantee zero bugs in every scenario.
Rust reduces memory bugs, though unsafe blocks mean you must still be careful; no language guarantees zero bugs.
What is the borrow checker and why is it important?
The borrow checker enforces rules about aliasing and lifetimes, ensuring references are always valid. This prevents data races and dangling pointers, which are common sources of bugs in C codebases.
The borrow checker stops invalid references and data races before code runs.
Is Rust slower to compile than C?
Rust can have longer compilation times, especially for large projects, due to extensive safety checks. However, once compiled, Rust typically delivers competitive performance comparable to optimized C.
Yes, Rust may take longer to compile, but run-time performance is often on par with C.
How does Rust handle unsafe operations?
Unsafe in Rust allows low-level access but is opt-in and contained. It requires explicit acknowledgment and careful review, preserving safety in the rest of the codebase.
Unsafe blocks are explicit and limited to where you need them.
Should I rewrite existing C code in Rust to improve safety?
A rewrite can improve safety and long-term maintenance, but it should be staged. Start with critical components and gradually migrate, weighing cost, risk, and added safety.
Consider a phased Rust migration for safety gains without risking the whole project.
Quick Summary
- Adopt Rust for safer memory management and concurrency
- Leverage Cargo and Clippy to enforce safety standards
- Understand ownership to prevent common bugs
- Plan phased Rust adoption for legacy codebases
- Evaluate domain constraints before choosing between Rust and C